- Halloween Jack-O-Lantern Bag
- $ 156.00
- MK purse
- $ 156.00
- 18K Gold Ring Without Diamonds
- $ 155.69
- 925 Silver Earrings
- $ 157.56
- A number 17 silver bracelet
- $ 157.94
- Ring
- $ 156.75
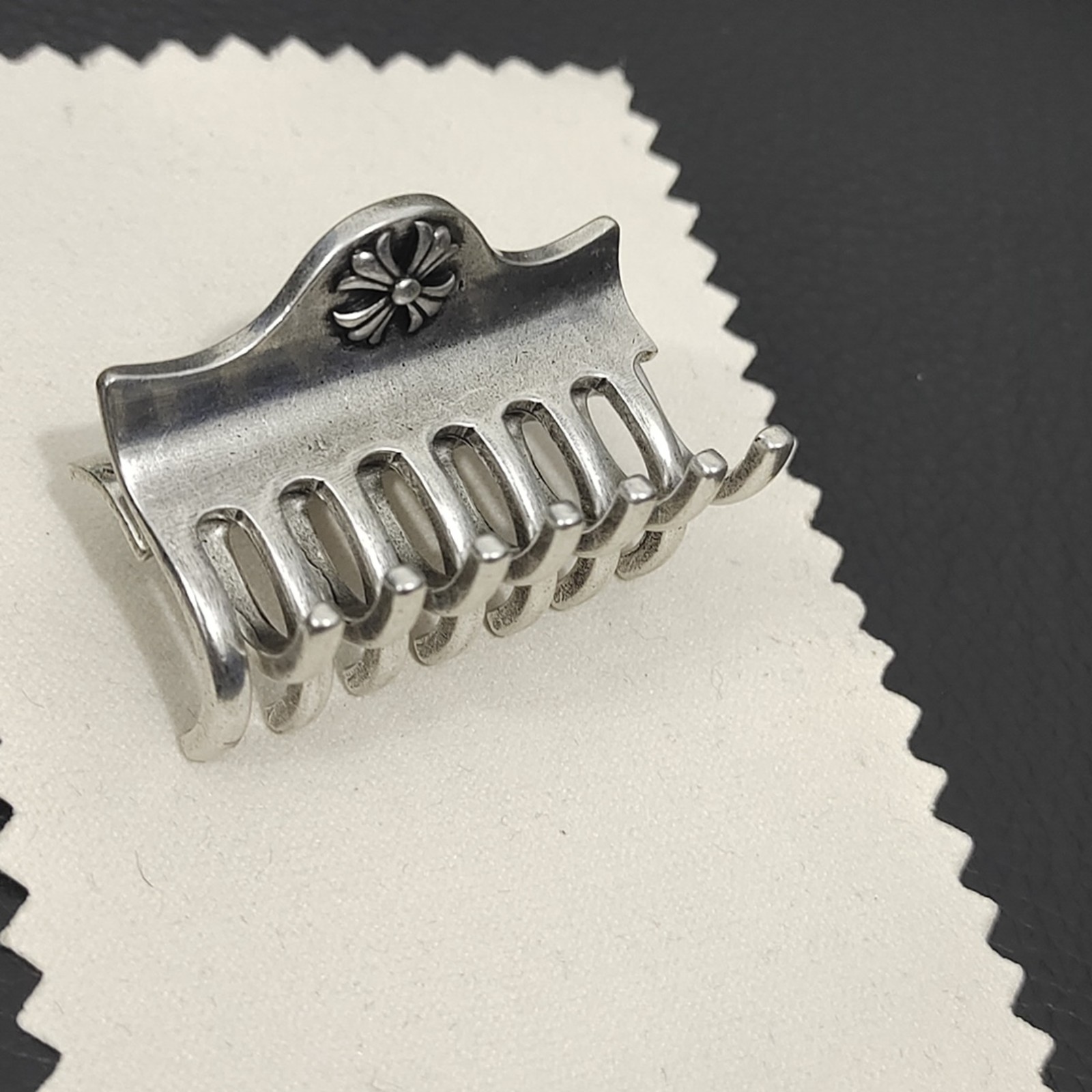
- Silver metal cross bobby pin
- $ 156.00
- Gold plated brass chain necklace
- $ 158.00
- Snow shield necklace
- $ 157.00
- Paris Tower necklace
- $ 158.00
- Vintage Hexagram necklace
- $ 156.00
- Unique hand made rings
- $ 158.00
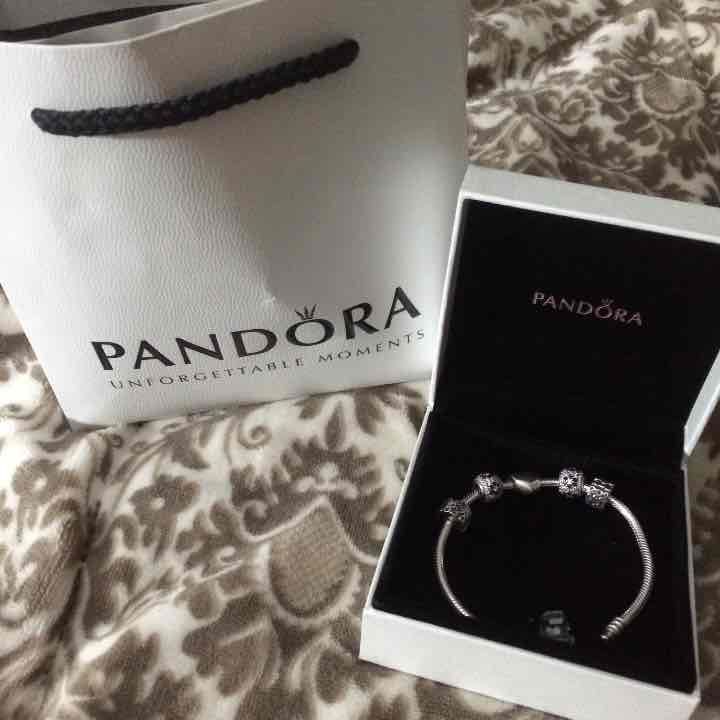
- Pandora charm bracelet
- $ 156.00
- Necklace and earrings
- $ 157.00
- Mermaid
- $ 157.00
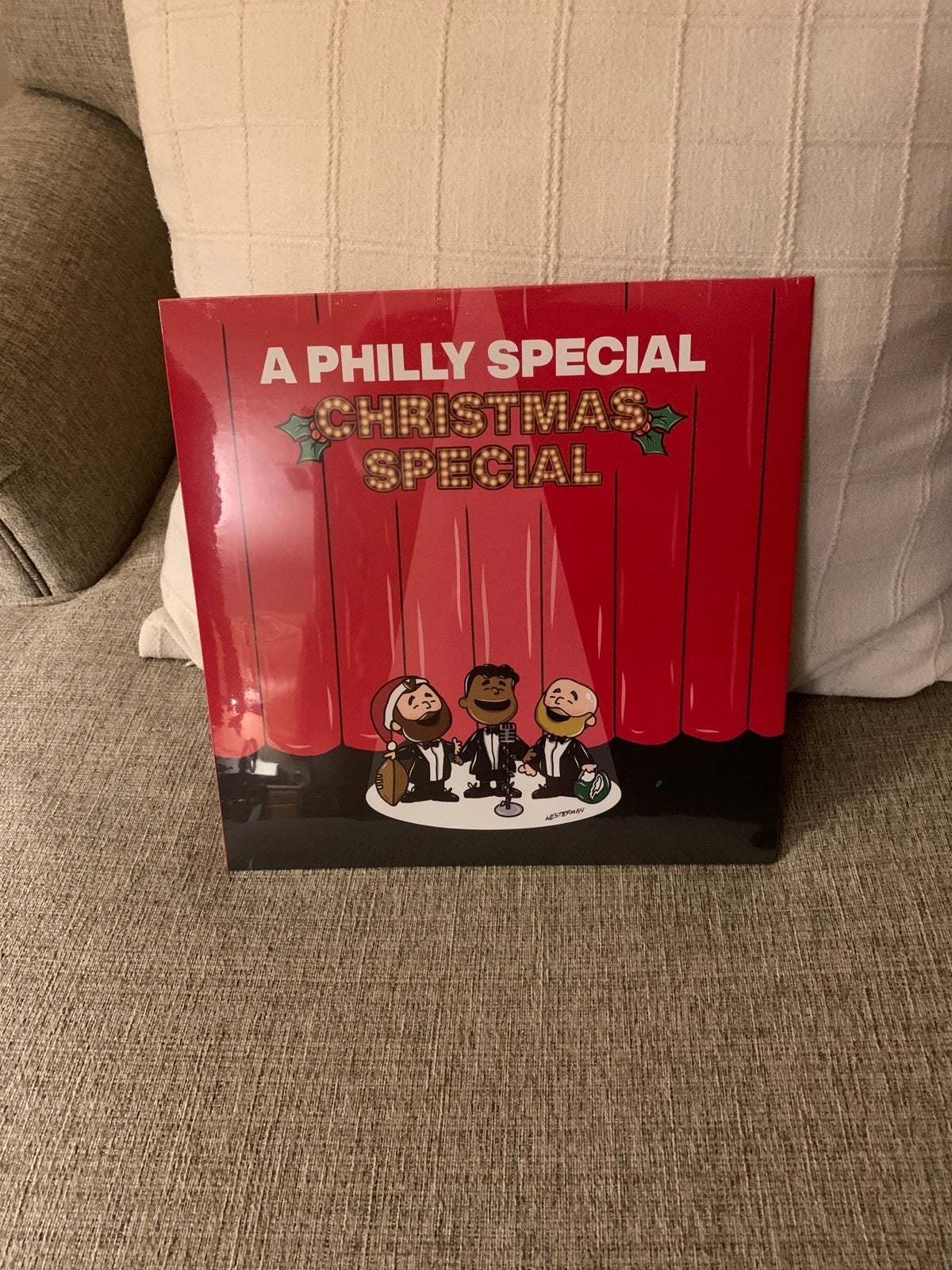
- A Philly Special Christmas Album #1
- $ 155.67
- Brian Eno Cassette Lot Rare
- $ 157.94